Improving encryption on old red hat 5 by new Oracle Linux 7 using apache mod_proxy
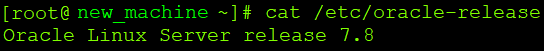
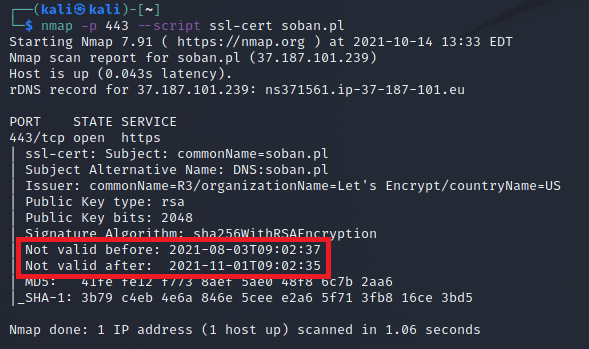
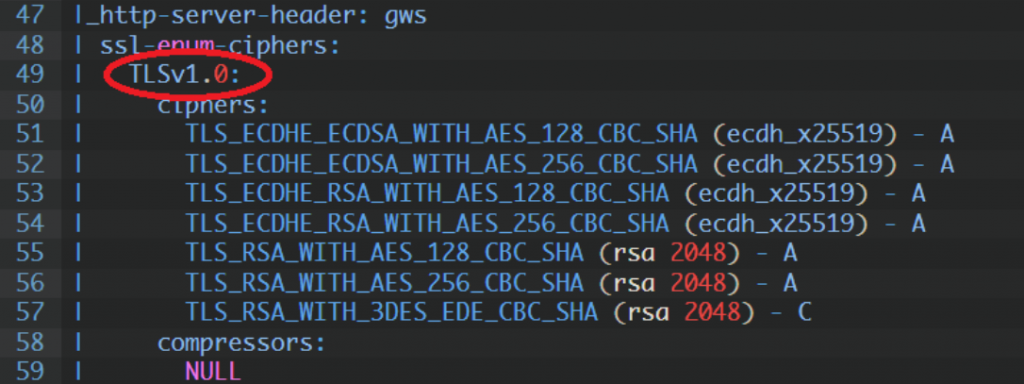
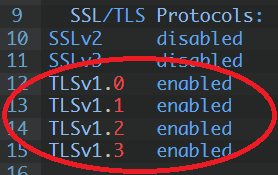
There are situations when we need to increase the encryption level on the old system – according to the PCI audit requirements. However, the old system is no longer supported, so updating the encryption level is not possible. This is not a recommended solution, because we should try to transfer the application to a new […]