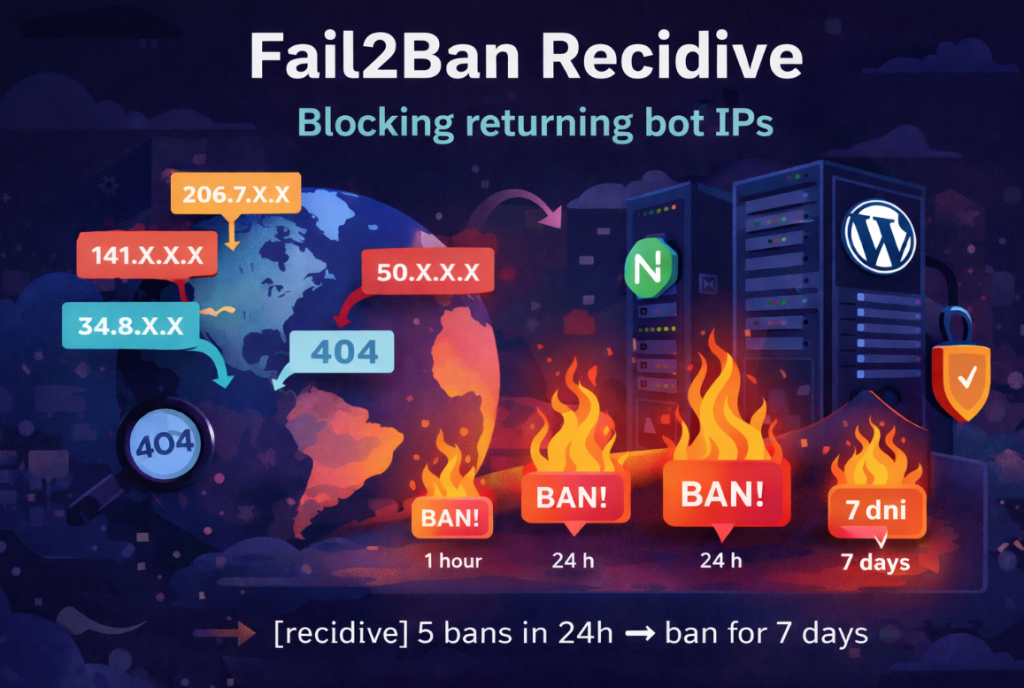
If you use Fail2Ban with Nginx and WordPress, sooner or later you’ll notice one thing: the same IP addresses keep coming back. They get banned for a few minutes or an hour, disappear… and shortly after try again /.env, /wp-login.php, /phpmyadmin, or other common attack paths.
The solution is not to aggressively tighten the filters. The solution is recidive — a second layer of protection in Fail2Ban that analyzes the ban history and blocks repeat offenders long-term.
Reference to the previous configuration
If you don’t yet have a basic Fail2Ban configuration for Nginx and WordPress, I described it here:
Fail2Ban + Nginx + WordPress – basic configuration
In that article, we configure jails such as nginx-exploit, nginx-secure, and sshd. Recidive does not replace that configuration — it strengthens it.
How to find repeat offenders in the logs
First, it’s worth checking whether the issue actually exists. We extract from the Fail2Ban logs the list of IP addresses that were banned most frequently:
|
1 |
grep "Ban " /var/log/fail2ban.log | awk '{print $NF}' | sort | uniq -c | sort -nr | head |
Example output (addresses partially anonymized):
|
1 2 3 4 5 6 7 8 9 10 |
13 204.76.203.18 9 41.142.XXX.XXX 8 64.89.XXX.XXX 8 50.82.XXX.XXX 8 35.243.XXX.XXX 8 34.24.XXX.XXX 7 45.166.XXX.XXX 7 34.83.XXX.XXX 7 176.42.XXX.XXX 6 49.36.XXX.XXX |
If you see numbers like 8, 9, or 13 — it means those IPs are coming back after the ban expires. A short bantime is just a technical pause for them.
Why recidive is better than increasing bantime
- You don’t have to ban everyone for 24 hours because of a single typo in a URL.
- You don’t increase the risk of blocking legitimate users.
- The penalty is progressive and applies only to returning addresses.
Recidive analyzes /var/log/fail2ban.log and counts how many times a given IP has been banned by other jails. This way, you only “finish off” those that have already been blocked multiple times before.
Recidive configuration (5 bans in 24h = 7 days ban)
Add the following block to /etc/fail2ban/jail.local:
|
1 |
nano /etc/fail2ban/jail.local |
At the end of the file, paste:
|
1 2 3 4 5 6 |
[recidive] enabled = true logpath = /var/log/fail2ban.log bantime = 7d findtime = 1d maxretry = 5 |
Save the file and restart Fail2Ban:
|
1 |
systemctl restart fail2ban |
Check the jail status:
|
1 |
fail2ban-client status recidive |
How to check who is close to the recidive threshold
If you want to see IPs that already have several bans and are approaching the recidive threshold:
|
1 |
grep "Ban " /var/log/fail2ban.log | awk '{print $NF}' | sort | uniq -c | awk '$1 >= 3 {print}' | sort -nr |
Summary
Recidive is one of the simplest and most effective ways to limit recurring scanners and bots. Instead of aggressively banning everyone — you block only those who repeatedly come back.
In an environment with multiple domains, Nginx reverse proxy, and WordPress, it’s practically a must-have configuration element: less noise in logs, fewer repeated attacks, and less manual analysis.